For decades, our identities have been tethered to tangible, physical objects. A flimsy piece of plastic defines our driving privileges, a government-issued card confirms our citizenship, and a wallet stuffed with various membership cards dictates our commercial affiliations. This system, however, is fraught with inefficiencies and vulnerabilities. The loss of a wallet is not just a financial inconvenience; it is an identity crisis, a bureaucratic nightmare of replacing essential documents. We stand at the precipice of a monumental shift, a revolution quietly unfolding in the palms of our hands. The humble digital wallet, once a novelty for contactless payments, is rapidly evolving into a secure, versatile, and powerful vessel for our entire digital selves, poised to render physical identities obsolete.
This transformation is not merely about convenience; it is a fundamental re-architecture of how we prove who we are in an increasingly digital world. It represents a convergence of technology, security, and user-centric design that promises to streamline interactions with governments, financial institutions, and businesses. This in-depth exploration will dissect the drivers of this revolution, the sophisticated technology underpinning it, the profound benefits it offers, the significant challenges it must overcome, and a glimpse into the future where your identity is seamlessly integrated into the digital fabric of your life.
A. The Inevitable Shift: Why Physical IDs Are Becoming Obsolete
The move away from physical identities is not a matter of if, but when. The limitations of the current system are becoming increasingly apparent in a world that operates at digital speed.
-
The Fragility and Inconvenience of Physical Documents: A physical ID card can be lost, stolen, damaged, or simply forgotten. The process of replacement is often time-consuming, expensive, and requires presenting other physical documents, creating a frustrating circular dependency. A digital identity, stored securely in a cloud-backed wallet on a device you always carry, is inherently more resilient and accessible.
-
The Security Paradox of Plastic: A driver’s license contains a wealth of personal information—your full name, address, date of birth, and even your photograph. In the wrong hands, this single document is a goldmine for identity thieves. Furthermore, the security features (holograms, micro-printing) are static and can be forged with increasing sophistication. Digital identities introduce dynamic, cryptographic security that is exponentially harder to replicate.
-
Inefficiency in Verification: Whether you’re renting a car, opening a bank account, or verifying your age at a bar, the process is manual. A person must physically inspect your ID, a process prone to human error and fraud. Digital wallets enable instant, machine-verifiable authentication, reducing friction and enhancing accuracy.
-
The Demands of a Digital-First Economy: The COVID-19 pandemic accelerated the adoption of remote services for healthcare, banking, and government aid. Trying to verify identity for a telehealth appointment using a physical document is clunky and insecure. The digital economy requires a native digital identity solution, and the wallet is the perfect container.
B. The Engine of Change: Core Technologies Powering Digital Identity Wallets

The transition from physical to digital identity is not powered by a single technology, but by a powerful synergy of several advanced systems.
A. Biometric Authentication: The Key to the Vault
The foundation of a secure digital identity wallet is robust authentication. Biometrics have become the gold standard, transforming your unique physical characteristics into the key that unlocks your identity.
-
Fingerprint Scanners: Now ubiquitous on smartphones, providing a fast and reliable first layer of security.
-
Facial Recognition: Systems like Apple’s Face ID or Android’s Face Unlock use sophisticated 3D mapping and infrared cameras to create a detailed depth map of your face, making it extremely difficult to spoof with a photograph.
-
Iris Scanners: While less common in consumer devices, iris patterns are even more unique than fingerprints, offering an additional layer of security for high-sensitivity applications.
B. Public Key Infrastructure (PKI): The Digital Notary
PKI is the cryptographic backbone that gives digital credentials their trust and verifiability. It works through a pair of keys: a private key that remains securely stored on your device and never leaves it, and a public key that is shared. When an organization issues you a digital driver’s license, they sign it with their private key. Any verifier (like a police officer) can use the issuer’s public key to confirm the license is authentic and has not been tampered with. This creates a chain of trust without ever exposing your underlying personal data.
C. Decentralized Identity (DID) and Blockchain: Taking Back Control
This is perhaps the most revolutionary concept. Instead of your identity being siloed with every service you use (your bank, your social media, your government), Decentralized Identity models give you back control.
-
How it Works: You hold your core identity attributes (like your name, age, and address) in your digital wallet. These are signed by trusted issuers (e.g., the DMV). When a service needs to verify, for example, that you are over 18, your wallet presents a cryptographically verifiable credential that proves this fact without revealing your exact birth date or other unnecessary information. This “selective disclosure” is a privacy game-changer.
-
Blockchain’s Role: While not always necessary, a blockchain can serve as a public, tamper-proof ledger for the public keys of trusted issuers. This allows anyone to verify that the credential came from a legitimate source without a central authority, enhancing trust and interoperability.
D. Secure Element Hardware: The Fort Knox in Your Pocket
Modern smartphones contain a dedicated, isolated chip called a Secure Element (SE). This is a hardware-based vault separate from the main operating system. Your private keys, biometric templates, and most sensitive credentials are stored here. Even if your phone’s OS is compromised by malware, the attacker cannot access the data stored in the Secure Element, providing a formidable barrier against digital theft.
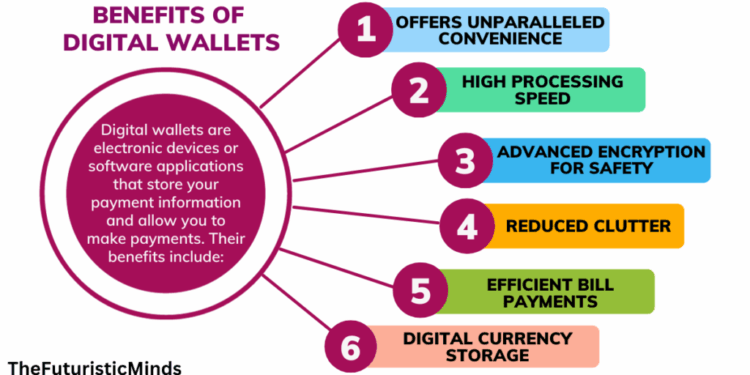
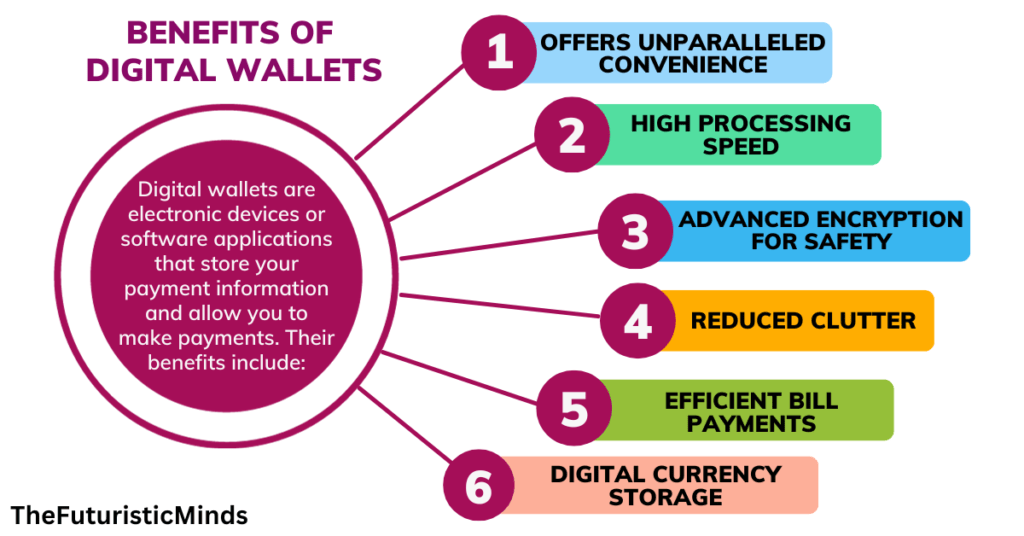
C. The Tangible Benefits: Why This Revolution Matters for Everyone
The adoption of digital identity wallets promises a cascade of benefits for individuals, businesses, and governments alike.
A. For the Individual: Unparalleled Convenience and Control
-
Consolidation and Simplicity: Your driver’s license, passport, health insurance card, loyalty cards, and payment methods all reside in one, always-accessible place.
-
Streamlined Interactions: Imagine tapping your phone to check into a flight, enter a secure building, or verify your age for a purchase. The process becomes instantaneous.
-
Enhanced Privacy and Selective Disclosure: You only share what is necessary. Need to prove you’re over 21? Share a “Yes/Over 21” credential, not your entire birth date. This minimizes data exposure and reduces tracking.
-
Reduced Identity Theft Risk: With biometrics and cryptography, stealing your identity becomes a computational nightmare compared to stealing a physical wallet.
B. For Businesses and Service Providers: Efficiency and Trust
-
Faster and Cheaper Onboarding: Automating customer identity verification (KYC) slashes administrative costs and reduces onboarding time from days to minutes.
-
Reduced Fraud: Verifiable digital credentials are extremely difficult to forge, reducing losses from fake IDs and synthetic identity fraud.
-
Improved Customer Experience: Frictionless checkouts and verifications lead to higher customer satisfaction and loyalty.
-
Regulatory Compliance: Digital audit trails from verified credentials can simplify compliance with regulations like GDPR or anti-money laundering laws.
C. For Governments and Public Sector: Modernization and Inclusion
-
Reduced Bureaucracy: Governments can issue and renew documents digitally, saving printing and distribution costs while speeding up services.
-
Enhanced Social Welfare: Digital IDs can streamline the distribution of benefits, ensuring they reach the right people efficiently and reducing leakage.
-
Financial Inclusion: For the billions of people worldwide who lack formal identification but have access to a mobile phone, digital wallets can provide a gateway to banking, education, and essential services.
D. Navigating the Obstacle Course: Challenges and Considerations
Despite the immense potential, the path to widespread adoption is not without significant hurdles that must be carefully addressed.
A. The Digital Divide and Accessibility
A system reliant on smartphones and digital literacy inherently risks excluding vulnerable populations, including the elderly, the poor, and those in rural areas with poor connectivity. A hybrid model, where physical backups or assisted digital services remain available, is crucial during the transition to ensure no one is left behind.
B. Privacy and Data Security Concerns
Centralizing our most sensitive identity data in one place creates a tantalizing target for hackers. While the security technologies are robust, the question of who has access to the data and how it is used is paramount. Strong, transparent data protection laws and clear user consent mechanisms are non-negotiable. The decentralized identity model is a promising solution, as it prevents the creation of a central honeypot of data.
C. Interoperability and Standardization
For digital wallets to work globally, they need to speak the same language. A digital driver’s license from California must be verifiable by a police officer in Florida, and ideally, a digital passport from Japan should be readable at an airport in Germany. This requires global cooperation on technical standards, trust frameworks, and legal recognition. Competing standards from tech giants like Apple and Google could potentially fragment the ecosystem.
D. Legal and Regulatory Frameworks
Laws in many countries were written with physical documents in mind. Legislatures need to update laws to give digital credentials the same legal standing as their physical counterparts. This includes defining liability in cases of theft, system failure, or verification errors.
E. User Trust and Behavioral Change
Perhaps the biggest challenge is psychological. People are accustomed to the tangibility of a plastic card. Convincing them to trust a digital representation requires a flawless security track record, transparent communication, and intuitive user experiences that demonstrably improve their daily lives.
E. The Future Unveiled: What Lies Beyond the Digital ID
The digital identity wallet is not the endgame; it is the foundational platform for a more profound transformation. As this technology matures, we can expect to see:
-
The “Self-Sovereign Identity” (SSI) Ecosystem: Users will become the true owners and managers of their identity data, issuing and revoking access to their attributes from a personal digital wallet, breaking the dominance of big tech and data brokers.
-
Seamless Smart Environment Integration: Your digital wallet will interact seamlessly with smart cities, your car, and your home. Your car will know your insurance and registration are valid. Your smart home will adjust settings automatically for recognized residents.
-
Verifiable Credentials for Qualifications: Academic degrees, professional licenses, and employment histories will become instantly verifiable digital credentials, streamlining job applications and professional mobility.
-
The Rise of the “Programmable” Identity: Your wallet could automatically assert specific attributes in predefined contexts. For instance, it could prove your membership to a gym at the door or your professional certification when logging into a industry-specific software.
Conclusion: An Inevitable and Empowering Transition
The replacement of physical identities by digital wallets is more than a technological upgrade; it is a societal paradigm shift. It represents a move away from fragmented, insecure, and inefficient forms of identification towards a unified, secure, and user-centric model. While the journey is complex, fraught with technical, regulatory, and social challenges, the destination is too compelling to ignore. A world where you can prove your identity, your qualifications, and your rights with a simple, secure tap of your phone is a world with less fraud, less bureaucracy, and more individual autonomy. The revolution is already in your pocket; it’s only a matter of time before it becomes the new normal.