For decades, our digital existence has been a fractured, insecure, and often frustrating experience. We are burdened with a seemingly endless list of usernames and passwords, our personal data is scattered across hundreds of corporate servers vulnerable to breaches, and proving who we are online requires a laborious process of uploading physical documents to faceless portals. This digital paradigm, built on a foundation of centralized control and siloed information, is fundamentally broken. However, a profound shift is underway a transformation so significant that it can only be described as the Digital Identity Revolution. This movement promises to return control and ownership of personal information to the individual, reshaping our interactions with governments, corporations, and each other in the digital realm.
The revolution is not about creating a digital clone; it is about establishing a secure, portable, and verifiable means of expressing our identity in the online world. It’s the difference between handing over your passport to a stranger who keeps a copy forever versus simply flashing a verified, tamper-proof badge that says, “Yes, I am over 18,” without revealing your birthdate, address, or nationality. This shift from centralized identity to self-sovereign identity (SSI) is the core of this upheaval, and its implications are as vast as the internet itself.
A. The Broken Foundation: Why Our Current Digital Identity Model is Unsustainable
To appreciate the revolution, we must first diagnose the disease of the current system. Our present model of digital identity is a relic of the early internet, designed for convenience rather than security or user autonomy.
A. The Password Predicament: The average internet user manages over 100 online accounts. This leads to password fatigue, where individuals reuse simple passwords across multiple sites. A breach at one minor service can compromise a user’s email, banking, and social media accounts if the same credentials are used. Despite advancements like two-factor authentication, the fundamental flaw remains: we are authenticating with “what we know” (a password) instead of “who we are.”
B. The Siloed Data Model: Every time you create a new account on a social media platform, an e-commerce site, or a government service, you create a new digital identity fragment. This company becomes the custodian and de facto owner of that slice of your identity. Your data is locked within their server, often used for targeted advertising without your explicit, informed consent. You have no direct control over it; you can only hope they protect it.
C. Data Breaches and Identity Theft: Centralized servers are honeypots for hackers. A single vulnerability can expose the personal information of millions of users. The Equifax breach of 2017, which compromised the data of 147 million people, is a stark reminder of the systemic risk. In this model, our identity is not ours to protect; it’s held hostage by the security protocols of the organizations we are forced to trust.
D. The Inefficiency of Verification: Applying for a loan, opening a bank account, or even signing up for a new mobile plan often requires a laborious process of identity verification. You must dig out physical documents, take pictures or scans, and upload them to a portal. This process is slow, expensive for the verifying company, and prone to fraud through forged documents. It creates friction that hinders economic activity and access to services.
B. The Pillars of Change: Core Technologies Powering the Revolution
The Digital Identity Revolution is not built on a single technology, but rather a powerful convergence of several key innovations that together create a new, trustable framework for identity.
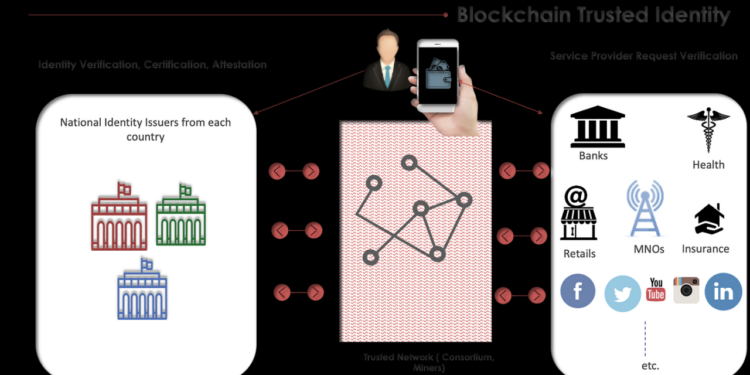
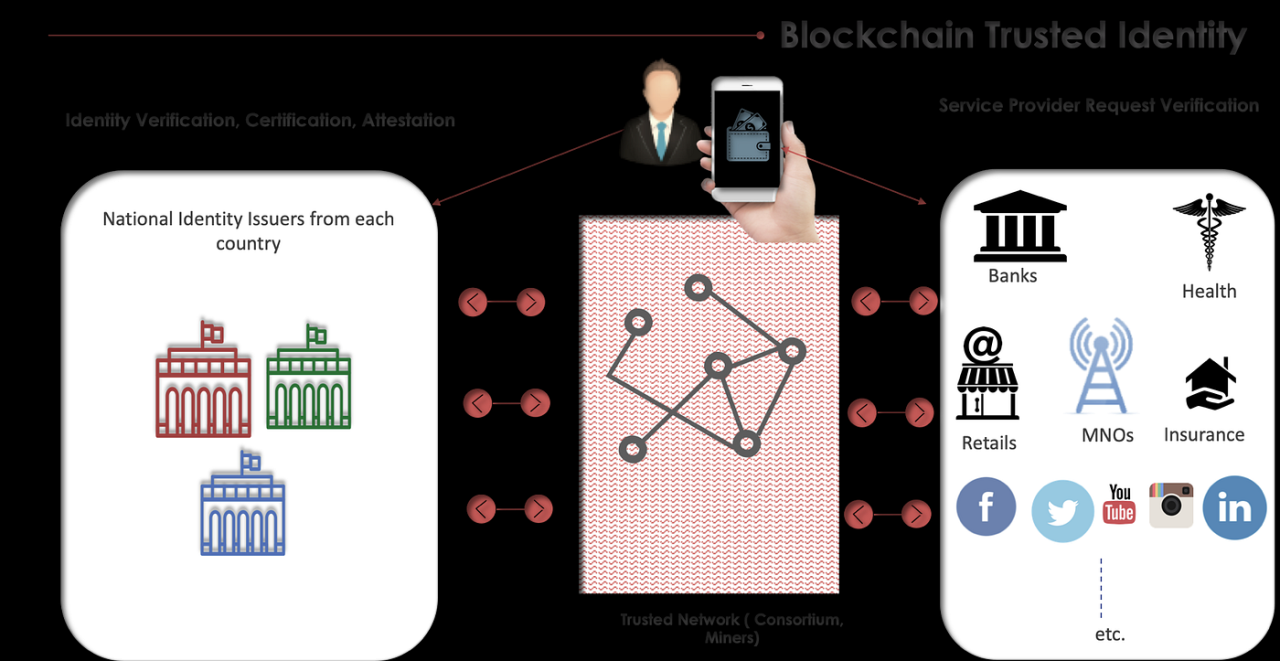
A. Blockchain and Distributed Ledger Technology (DLT): At the heart of the revolution lies blockchain. Its core properties decentralization, immutability, and transparency provide the perfect foundation for a new identity layer. Instead of a single company holding your data, the “root of trust” is distributed across a network of computers. No single entity can control it or take it down. The blockchain is not used to store personal data (like your name or address), but rather to store the cryptographic proofs and public keys that act as anchors for verifiable credentials. This creates a global, permissionless system for trust.
B. Verifiable Credentials (VCs): These are the digital equivalent of physical credentials like your driver’s license or university degree. A trusted issuer (e.g., a government agency, a university) can cryptographically sign a credential and issue it to your digital wallet. This credential is tamper-proof and can be independently verified by anyone without needing to contact the issuer directly. For example, your digital driver’s license VC would cryptographically prove it was issued by the DMV and has not been altered.
C. Decentralized Identifiers (DIDs): These are the new user-centric identifiers for the digital world. A DID is a globally unique string that you generate and own, independent of any centralized registry, identity provider, or certificate authority. You can have multiple DIDs for different contexts (e.g., one for professional life, one for social media) to maintain privacy. DIDs are stored on a blockchain and are used to sign and authenticate Verifiable Credentials, proving you are the legitimate holder.
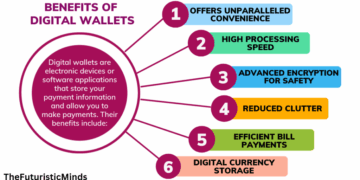
D. Digital Wallets: This is the user-facing application that puts you in control. A digital wallet on your smartphone is where you store your DIDs and your collection of Verifiable Credentials. It is a secure vault that you control with your own private keys. When a service asks for proof of your age, you, the owner, choose which credential to present from your wallet and grant permission for its use. The data never leaves your possession without your consent.
C. The New Paradigm in Action: A Step-by-Step Journey of SSI
Let’s illustrate how this works in a real-world scenario: renting an apartment.
-
Issuance: The Department of Motor Vehicles (DMV), acting as an Issuer, gives you a Verifiable Credential for your driver’s license. They cryptographically sign it with their private key and send it to your digital wallet. The credential contains attributes like your name, date of birth, and address.
-
Storage: You, the Holder, store this VC securely in your digital wallet, which is linked to your Decentralized Identifier (DID).
-
Verification Request: You apply for an apartment online. The landlord (the Verifier) needs proof of your identity and credit score. Instead of asking for physical documents, their website requests a Verifiable Presentation. Specifically, they ask for: A) Proof of government-issued ID. B) Proof of credit score above 700.
-
Consent and Presentation: You open your digital wallet. You see the landlord’s request. You consent to share the required information. Crucially, your wallet uses Zero-Knowledge Proofs (ZKPs) an advanced cryptographic technique—to create a presentation. You don’t have to show your entire driver’s license. You can prove you are over 18 without revealing your birthdate, and prove your credit score is above 700 without revealing the exact number. You create a Verifiable Presentation, sign it with your private key, and send it to the landlord.
-
Instant Verification: The landlord’s system instantly verifies two things: A) That the DMV’s signature on your VC is valid (using the DMV’s public key on the blockchain). B) That your presentation was signed by the holder of the DID (you). The verification is automatic, secure, and privacy-preserving.
This process eliminates fraud, reduces paperwork, speeds up the application, and gives you unprecedented control over your personal data.
D. The Far-Reaching Implications: How the Revolution Will Transform Industries
The impact of user-centric digital identity extends far beyond simplifying logins. It is a foundational technology that will disrupt numerous sectors.
A. Finance and Banking (DeFi & FinTech): The world of Decentralized Finance (DeFi) desperately needs secure identity to comply with regulations like KYC (Know Your Customer) and AML (Anti-Money Laundering) without compromising its decentralized ethos. SSI allows for portable KYC credentials. A user could complete a KYC check once with a trusted provider and then use that verifiable credential to access multiple DeFi protocols and centralized exchanges, streamlining onboarding and enhancing security while preserving privacy.
B. Healthcare: Patient data is notoriously siloed. With SSI, patients could own their health records as a collection of Verifiable Credentials from different providers. They could then grant temporary access to a new specialist or an insurance company, improving continuity of care, enabling medical research with patient consent, and giving individuals a comprehensive view of their own health history.
C. Supply Chain and Logistics: Verifiable Credentials can be assigned to physical products. A bottle of wine could have a digital twin with VCs proving its organic certification, origin, and temperature control throughout its journey. This creates an immutable chain of custody, drastically reducing counterfeit goods and ensuring product authenticity and quality for the end-consumer.
D. Government and Civic Participation: Governments can become issuers of foundational credentials like birth certificates, social security numbers, and business licenses. This would revolutionize citizen services, from applying for benefits to voting. Secure, remote digital voting, long a holy grail of digital governance, becomes a more plausible future reality with a robust digital identity framework.
E. The Gig Economy and Education: Freelancers could hold verifiable credentials for completed projects, skill certifications, and client reviews. This creates a portable, trustable reputation that is not tied to a single platform like Upwork or Fiverr. Similarly, universities can issue digital diplomas that cannot be forged, allowing graduates to instantly share their qualifications with employers worldwide.
E. Navigating the Challenges: Obstacles on the Path to Widespread Adoption
Despite its immense potential, the Digital Identity Revolution faces significant hurdles that must be overcome.
A. Standardization and Interoperability: For a global digital identity system to function, all players issuers, holders, and verifiers must use compatible standards. Organizations like the World Wide Web Consortium (W3C) are leading the charge in creating standards for DIDs and VCs, but widespread adoption by governments and large corporations is still needed.
B. User Experience and Accessibility: The technology is complex, but the user experience must be simple. The digital wallet must be as intuitive as a physical wallet. If the process is confusing or cumbersome, mainstream adoption will fail. Furthermore, solutions must be inclusive, ensuring that those without smartphones or reliable internet access are not left behind.
C. Legal and Regulatory Frameworks: The legal status of a digital driver’s license must be equivalent to its physical counterpart. Governments need to establish clear regulations that recognize electronic signatures and verifiable credentials as legally binding. Data privacy laws, like GDPR in Europe, must be harmonized with the principles of SSI to ensure compliance.
D. The Digital Divide: A revolution built on smartphones and internet access risks exacerbating the gap between the connected and the unconnected. Bridging this divide is a critical social challenge that must be addressed in parallel with the technological rollout.
E. The Phishing Threat Evolved: While SSI eliminates passwords, it introduces new attack vectors. If a user is tricked into signing a malicious transaction with their private key, the consequences could be severe. User education on key management and security will be paramount.
F. The Future Forged in Code: What Lies Ahead for Digital Identity

The Digital Identity Revolution is still in its early stages, but its trajectory is clear. We are moving towards a world where our digital selves are as integrated, secure, and under our control as our physical selves.
We can anticipate the emergence of “Identity Networks,” where reputation and trust become composable and portable across different platforms. Your responsible financial behavior in one ecosystem could become a verifiable credential that grants you better terms elsewhere. We will see the rise of AI and Identity, where autonomous agents and Internet of Things (IoT) devices will need their own DIDs to interact securely with each other and with humans.
The revolution is not merely a technological upgrade; it is a reclamation of a fundamental human right the right to control one’s own identity. It promises a future where we can navigate the digital world with the same confidence, privacy, and freedom we expect in the physical world. The journey has begun, and it is leading us toward a more equitable, efficient, and user-centric digital future for all.